IT policies are essential to effective deployment of technologies; they outline the path a business chooses to take, aligning action with actual goals. Policies can also help create a more trustworthy profile for a business by reinforcing that you take security seriously, both your own and that of your customers, and that you are committed to protecting it. Having policies in place also saves time and effort. In the absence of a clear understanding of security needs, businesses may enforce unnecessary standards in implementing rules and derailing efficiency and productivity. While businesses across most industries are encouraging work from home, a report in CISO MAG reveals that 60% of businesses do not have a cybersecurity policy.
Operating without a cybersecurity policy can compromise the business image and operations. Security policies highlight your commitment to risk preparedness, as well as your overall management of data and information.
What policies are critical for businesses?
IT policies apply to the users within an organization. They outline data security rules, measures, and procedures.
1. Acceptable Use Policy: This policy outlines general usage of equipment and handling of information for business and client operations. It also outlines data security measures — nobody within the business may access data unless it is needed as part of their job.
2. Incident Report Policy: This can be part of a business continuity plan; it details expected response to any incident involving security breaches. This policy typically identifies an incident response team, the individual to be contacted, and the procedure to be undertaken if an incident causes a data and information breach or compromise.
3. Information Security Policy: A comprehensive information security policy can help ensure data security measures are in place. This policy helps to ensure relevant resources are in place, such as hardware infrastructure and software. In addition, this policy ensures the recording of audit events, including failed attempts at logging into the system, start up or shut down, firewall anomalies, addition or removal of devices in the network, etc. An information security policy also typically outlines action or intended action to take based on audit events.
4. Change Management Policy: This policy outlines the recording of all changes made to the information system within the business. The aim is to make only necessary changes and those that add gainfully to the operations without negatively impacting services and deliverables.
5. Remote Access Policy: This policy covers connections to a business’s information system from any host. It outlines the provisions governing the sending and receiving of emails, as well as other intranet resources. Encryptions, software to prevent malware, secure log-outs, and connections with other networks are facets covered by this policy.
Securing the business
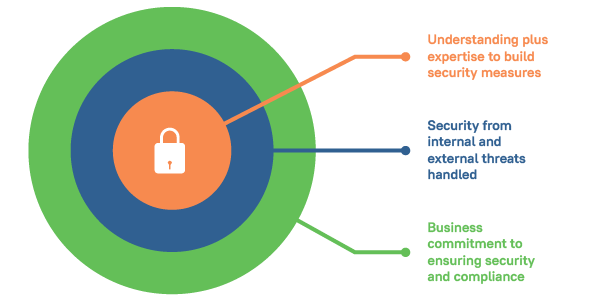
A Cyber Readiness Institute (CRI) report says that though small business owners are concerned about cyberattacks, they lack the resources to invest in the necessary security. For growing businesses, this can mean the difference between sustainability and business closure. Outsourcing the task to professionals can help businesses access critical and necessary expertise without compromising security. A robust IT system can help propel business goals by providing critical operational support where needed. Professional IT expertise can also help the business create the necessary policies. Judiciously handled digital asset management can help recovering small businesses and startups operate sustainably and plan for future growth.
Next steps
- Learn more about Analytix IT Solutions, with more than a decade of experience working with startups and small businesses, boosting capabilities and helping them ascend the growth curve.
- Email us at sales@analytix.com or call us on 781.503.9003 today.
- Follow our blog for industry trends and the latest updates.
- Engage with us on LinkedIn and Twitter.
