Endpoint security is more important than ever before. It’s no longer enough just to protect your device and data. You need to protect everything that connects to it—including employees’ laptops and personal smartphones. This article will explain why protecting endpoints is so critical, how you can do it effectively, and how one thing can still make or break your overall security strategy: visibility.
In business operations today, endpoints are the new battleground. Cybercriminals target endpoints for several reasons:
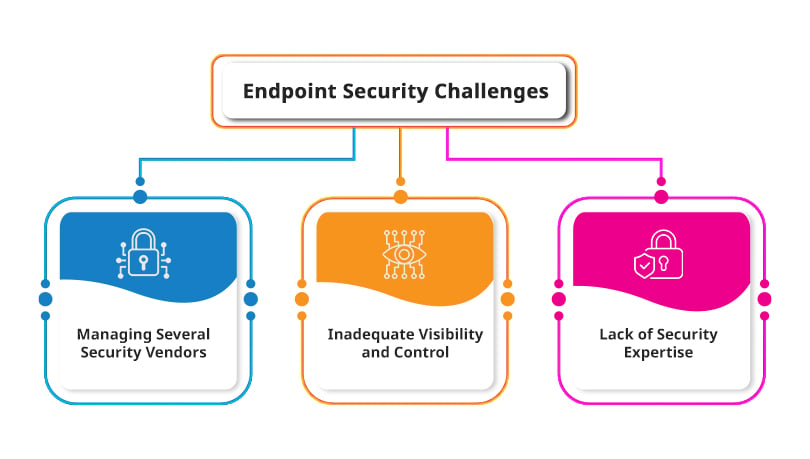
Endpoint security is a complex and difficult task. There are many challenges in protecting endpoints, which include:
Managing several security vendors is a challenge. Companies must always maintain an open dialogue with their vendors, which can be difficult when there are so many different products and services available. It’s also difficult to keep track of all the latest technology trends and the latest threats that hackers use against businesses.
The best way to deal with this problem is by choosing one vendor that provides you with everything you need, including audits and training programs on endpoint security. This will help ensure that your employees understand what they’re doing, how it affects them personally, and why they need to take certain actions within your organization (such as installing anti-virus software).
As the IT infrastructure of a business grows, it becomes more challenging to manage. For example, if you have several endpoints the sat are not managed by endpoint security solutions, you cannot know whether they contain any malicious software or viruses.
If you don’t have centralized visibility into your endpoints and access points (APs), it can be challenging to respond appropriately to threats in these areas. Anytime there is an infection in one of your devices, this could potentially spread throughout the rest of your network and lead to downtime for critical applications and systems. This may mean that users are unable to access their email accounts or file servers because a virus has infected them as well.
A comprehensive endpoint security strategy is critical to protecting your business. The threat landscape continues to evolve and change, so you need a strategy that covers all layers of the IT stack—from endpoints and networks to data centers and cloud environments.
If you’re not sure where, to begin with the process of securing your network against cybercriminals and malicious attacks, here are five key steps for building an effective endpoint security program:
In comparison, accounting professionals now typically request less access than before because they’re worried about security risks associated with open file-sharing protocols.
The concept of endpoint security is a new frontier for IT and business alike. It’s a challenge that requires taking risks and trying new things, but it also presents an opportunity for both parties to work together toward common goals.
Endpoint security is designed to protect the devices at which employees work—computers, tablets, smartphones—from attacks that may compromise their privacy or steal sensitive information. Endpoint protection is one piece of overall network protection; it helps ensure that systems are secure from malware or hackers while they’re being used by people on the Internet or at remote locations, such as telecommuters or traveling employees who use laptops for work.
While implementing an endpoint security strategy is challenging, it’s not impossible. With the right tools and expertise, you can create a comprehensive plan that protects your organization from the latest threats and helps your business keep data safe.